Category Archives: Articles
The Need for a SOC and The Importance of Security Services in Business Networks
A SOC works to improve the organization's overall cybersecurity through threat detection and prevention and [...]
Jun
Why Business Should Focus on Application Whitelisting
Application whitelisting is a security practice that allows only approved applications to run on a [...]
Jun
The Rise Of Bitcoin: What It Means For Business
The Rise Of Bitcoin: What It Means For Business With the adoption of blockchain technology [...]
Jul
The Consequences Of The Colonial Pipeline Ransomware Attack And The Effect It Had On DarkSide Hacking Group
The Consequences Of The Colonial Pipeline Ransomware Attack And The Effect It Had On DarkSide [...]
Jun
Colonial Pipeline Ransomware Attack: Why and What
Colonial Pipeline Ransomware Attack: Why It Can Happen To Anyone, Anytime, And What You Need [...]
May
How to double-check OneDrive sync
One Drive is the local application that syncs Windows or Mac to SharePoint through Office [...]
Mar
What Reddit Users Should Be Doing After the Hack (And General Password Safety Tips)
Did you catch wind of the most recent data hack? Yes—Reddit was hacked on August [...]
Aug
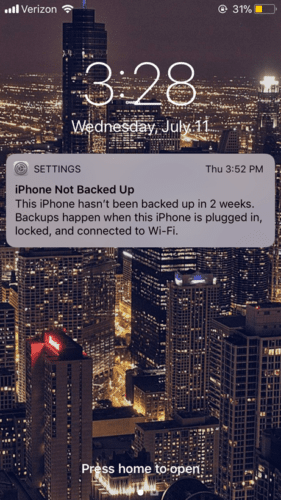
Have an iPhone? Make sure you don’t lose your pictures and contacts!
The information that we keep on our phones gets more and more important as time [...]
Jul
Slow Computers Cost Businesses Money
We developed this infographic to explain: Sources: http://www.cdc.gov/physicalactivity/data/facts.htm https://www.siliconrepublic.com/gear/slow-loading-pcs-waste-130-hours-per-year-cause-bad-moods-and-aggression
Jul
PAIN Point: Employee Efficiency
Many years ago, we had a client who used a tape drive as their data [...]
Jul